Responsible Disclosure: Reflected XSS (sanitized)
This is a responsible, vendor-safe writeup of a Reflected Cross-Site Scripting (XSS) issue identified during authorized testing. The content is intentionally sanitized: no raw payloads or sensitive values are published. If remediation validation is needed, I can share a minimal redacted PoC via an encrypted channel or the vendor’s secure portal.
Executive summary
A user-controlled input in a public endpoint is reflected into the HTML response without context-aware output encoding. In certain render contexts this allows attacker-supplied script to execute in the victim’s browser if they follow a crafted link. Immediate fixes include proper encoding/escaping, stricter Content Security Policy (CSP), and input normalization.
Observed endpoint & environment
- Endpoint (example):
/search-products.php(parameter observed:search) - Method: GET
- Environment: Production (reported by researcher)
- Authorization: Testing performed under permission
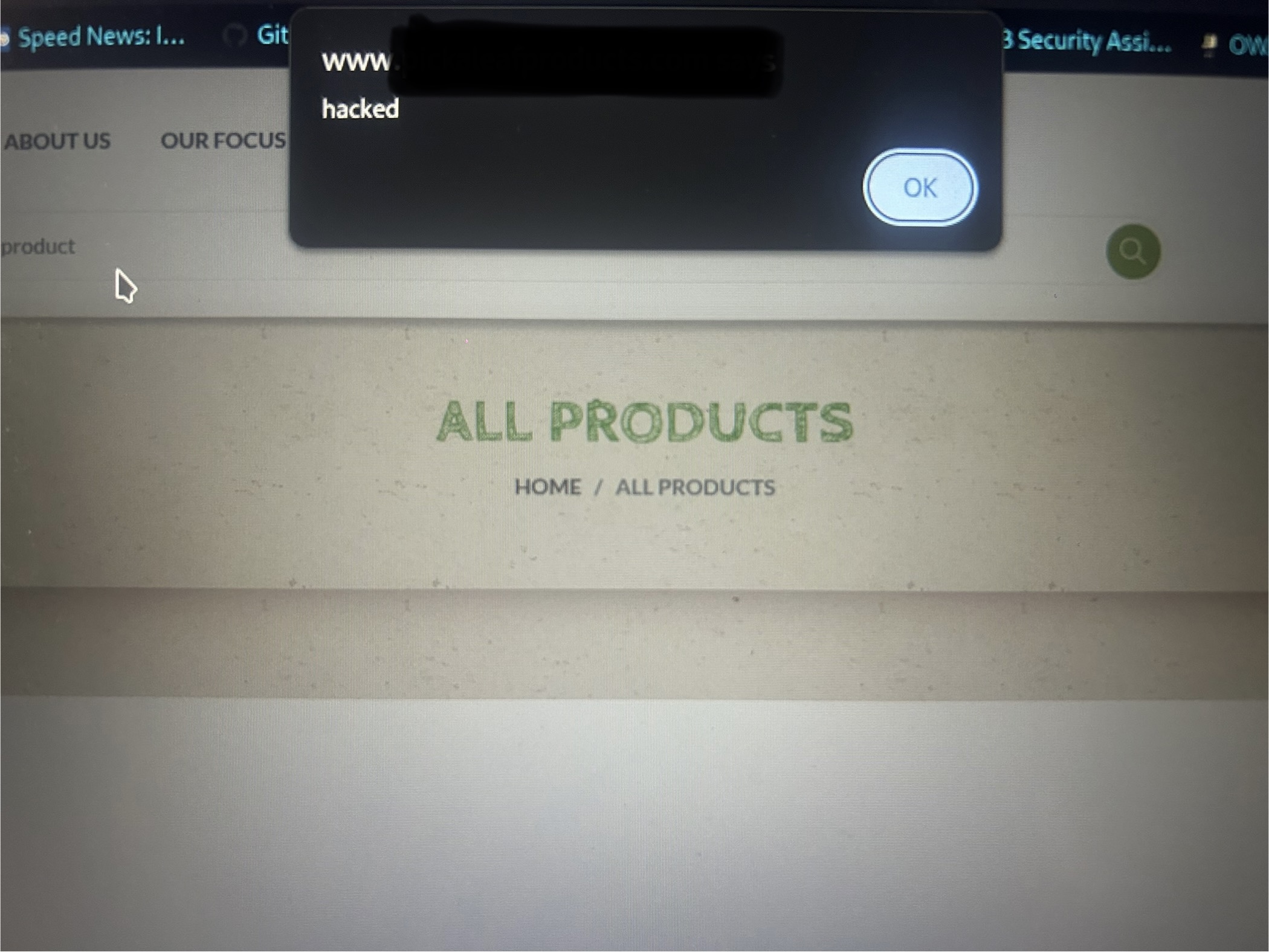
What I observed (sanitized)
The application echoes the provided search value directly into the page’s HTML. Because the output was not correctly encoded for the HTML context, a crafted value rendered in the browser in a way that allowed client-side script execution. Evidence below is redacted to remain vendor-safe.
Impact
- Execution of attacker-controlled JavaScript in a victim’s browser
- Risk of session token theft, UI spoofing, or forced actions (depending on app context)
- Damage to user trust and brand reputation via malicious links
Safe reproduction steps (for vendors/devs)
Note: Use staging or masked accounts — do not test with real user data.
- Identify where the search parameter is reflected in the response HTML.
- Render a clearly marked benign token and confirm the exact context (HTML node, attribute, script, or URL).
- Apply context-aware encoding and verify that the token renders as text rather than executable code.
Root cause (high level)
Untrusted input is inserted into server-generated HTML without context-aware output encoding. In addition, the page lacks a restrictive Content-Security-Policy that would reduce XSS impact.
Safe remediation (developer-focused)
1) Context-aware output encoding
<div>Search: <%= htmlEncode(userInput) %></div>
<input value="<%= attributeEncode(userInput) %>" />
<script>
const q = JSON.parse('<%= jsonEncode(userInput) %>');
</script>2) Enforce a restrictive CSP
Content-Security-Policy: default-src 'self'; script-src 'self'; object-src 'none'; base-uri 'self'; frame-ancestors 'none';3) Input normalization
- Trim control characters; limit length of search strings
- Allow-list expected characters for search (letters, digits, spaces)
- Consistently encode/escape wherever the value is rendered
Recommendations for immediate mitigation
- Temporarily filter/strip script-like tokens at the edge (WAF) while fixes ship
- Add security headers (CSP, X-Content-Type-Options, Referrer-Policy)
- Log and monitor unusual query strings and referrers
Suggested vendor contact (copyable)
Subject: Security report — Reflected XSS on [your-domain]
Hello,
I discovered a reflected XSS affecting (parameter: search). I can share sanitized screenshots and a minimal PoC via an encrypted channel or your secure upload portal.
Please acknowledge and provide your PGP key or secure link for evidence transfer.
Regards,
Aryan Pareek
CEH | Penetration Tester | The Cyber Aryan
aryanpareek311072004@gmail.com
Conclusion
Reflected XSS is common but preventable. The durable fix is context-aware encoding at every render point, backed by a strict CSP and input normalization. If you are the site owner, contact me via a secure channel — I’ll validate the patch and retest responsibly.