
STIG,NIST and ISO
The Holy Trinity of Not Getting Hacked (Or At Least Looking Like You Care)
Read Full Blog →
The Holy Trinity of Not Getting Hacked (Or At Least Looking Like You Care)
Read Full Blog →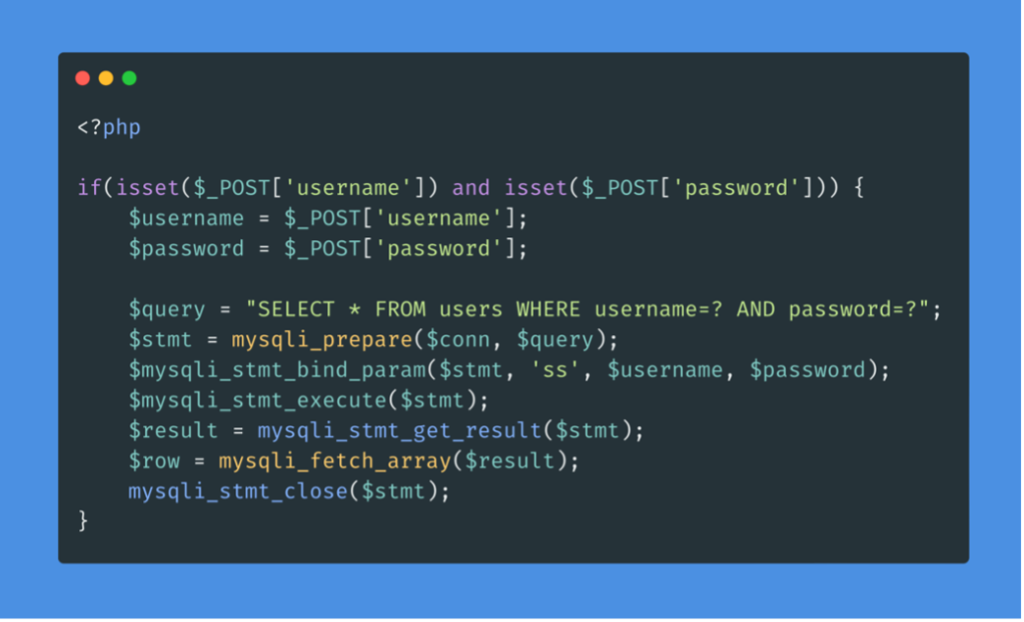
A vendor-safe case study of a discovered SQL Injection in a public endpoint. This post contains sanitized PoC notes, safe reproduction steps for developers, and remediation guidance using prepared statements. Screenshots are redacted for privacy.
Read Full Blog →
A compact, high-efficiency toolkit for real engagements: Burp Suite, nmap, gobuster, Nikto, and custom Bash scripts for recon. I explain when to use each and provide quick config tips.
Read Full Blog →
Bots or zombies? A simple explanation of how botnets work and how attackers use them.
Read Full Blog →
Look, we all know about Metasploit, Burp Suite, and Nmap. They're the "popular kids" of the cybersecurity world—everyone talks about them, everyone uses them, and honestly? They get all the attention they deserve. But here's the thing: the real gems are hiding in plain sight, gathering dust in GitHub repositories while everyone's busy flexing their Kali Linux boxes
Read Full Blog →
IDOR (or BOLA) explained with simple examples and real‑world scenarios.
Read Full Blog →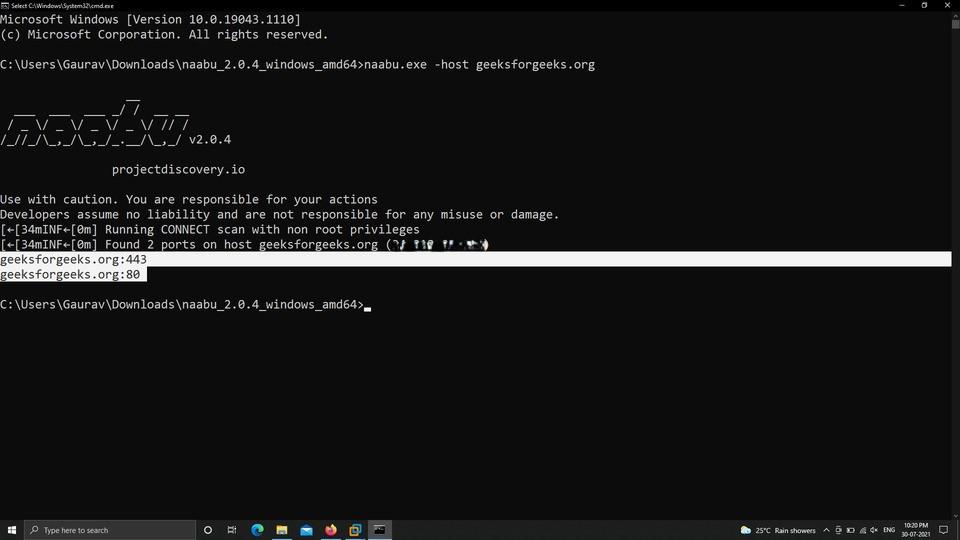
A complete beginner‑friendly guide to Naabu for fast port scanning.
Read Full Blog →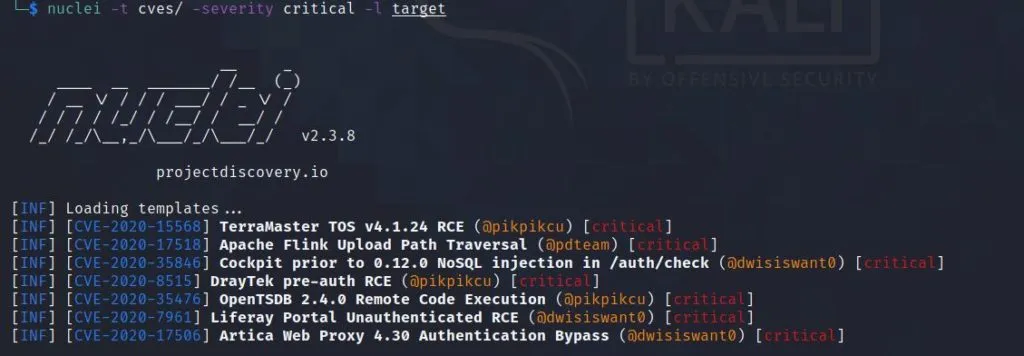
A detailed walkthrough of Nuclei templates, flags, and real usage.
Read Full Blog →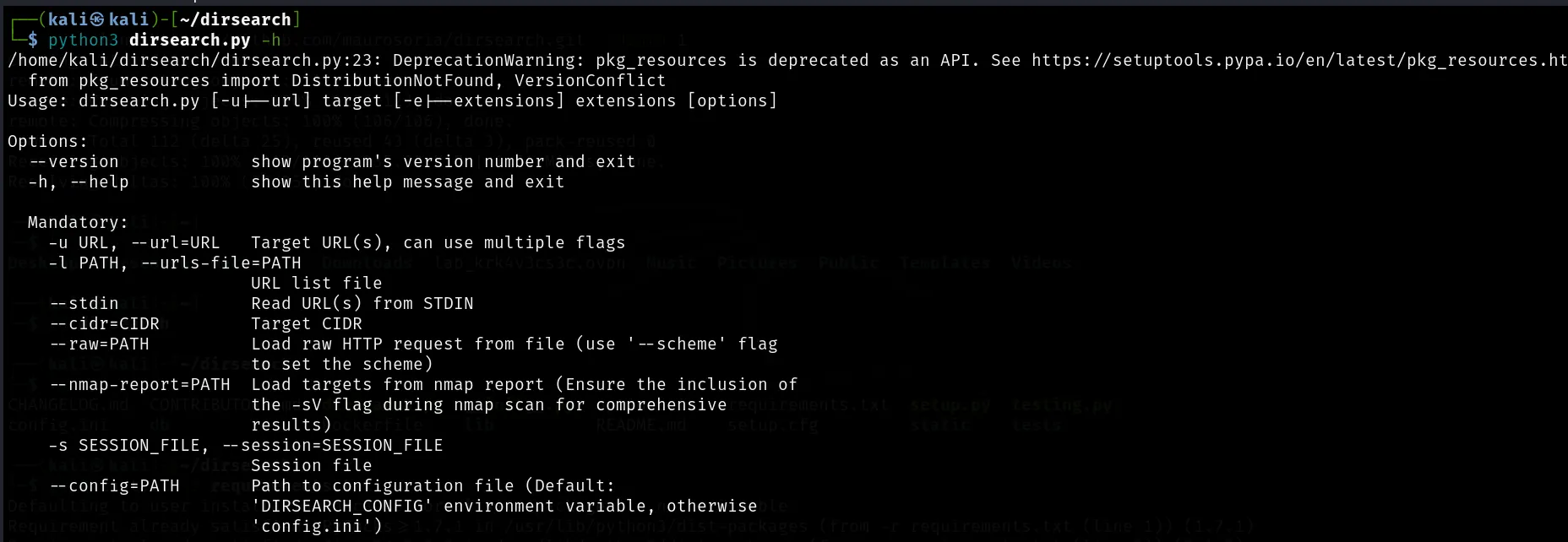
Learn directory enumeration with full commands and use‑cases.
Read Full Blog →
Key flags, scripts, and workflows for network scanning.
Read Full Blog →
Clear explanation of `../` attacks with safe examples.
Read Full Blog →
Fast host probing and automation for recon workflows.
Read Full Blog →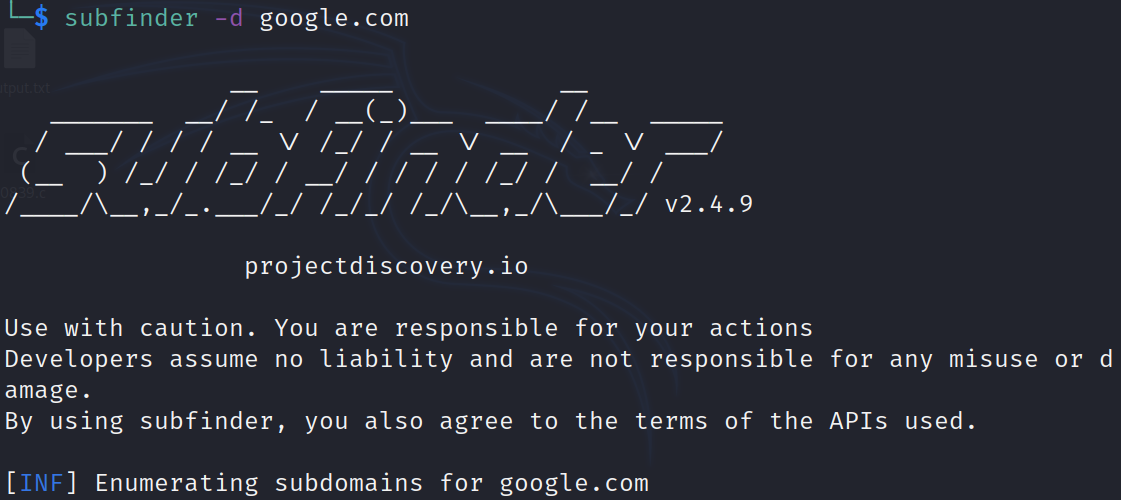
Passive subdomain enumeration explained in simple words.
Read Full Blog →
A safe, redacted XSS discovery explained step‑by‑step.
Read Full Blog →
A safe SQLi discovery walkthrough with remediation steps.
Read Full Blog→